The world of cryptocurrency offers unparalleled financial freedom and technological innovation, but it also operates outside traditional safety nets. In the crypto world, you are your own bank. This responsibility means that if your assets are compromised, there is no "customer support" to call for a refund. As we move further into 2026, the sophistication of digital thieves is reaching new heights. Protecting your wealth requires more than just a strong password; it requires a deep understanding of digital custody, network security, and common psychological scams.
1. The Foundation: What is Blockchain?
To secure your crypto, you must first understand what it is. A blockchain is a decentralized ledger that records all transactions across a network of computers. Unlike a bank, which is a single point of failure, the blockchain is verified by thousands of independent participants. When you "own" crypto, you don't actually own a file; you own the *private key* that allows you to move funds from your address on the ledger to another.
Understanding this "sovereign" nature of ownership is the first step toward security. If someone gets your key, they own your funds. There is no middleman to stop them. Safety in crypto starts with the realization that your private keys are the most valuable pieces of information you possess.
2. Choosing a Secure Exchange

Most beginners start by buying their first coins on a centralized exchange (CEX) like Coinbase or Binance. These are convenient, but they represent a major security risk: they hold your private keys for you. In the crypto community, the phrase "Not your keys, not your coins" is a cardinal rule. If the exchange is hacked or goes bankrupt, your funds could be lost forever.
While CEXs are great for trading, they shouldn't be used for long-term storage. Only keep assets on an exchange that you intend to trade in the immediate future. For everything else, you need to transition to a personal wallet where *you* hold the keys.
3. Private Keys & Cold Storage
The safest way to store cryptocurrency is in "Cold Storage"-a hardware wallet that is never connected to the internet. These devices (like Ledger or Trezor) keep your private keys offline, making it virtually impossible for remote hackers to steal them. Even when you plug the device into a computer to make a transaction, your keys never leave the secure hardware.
When you set up a hardware wallet, you'll receive a "Seed Phrase" (24 random words). This phrase is your ultimate backup. If you lose your device, you can recover your funds with this phrase. If someone *sees* this phrase, they can steal everything. Treat this phrase like a bar of solid gold-hide it in a physical safe, and *never* type it into a computer or take a photo of it.
4. Recognizing "Phishing" Scams

Phishing is the most common way crypto is stolen. Thieves create fake websites that look identical to your exchange or wallet provider, hoping you'll type in your login details or seed phrase. They often send emails or DMs claiming your account has been "locked" and you need to "verify" it immediately to save your funds.
Always bookmark the official URL of your exchange and never click links in emails. A legitimate company will *never* ask for your seed phrase. If you're being rushed or told there's an emergency, it's almost certainly a scam. Slow down, check the URL, and never give away your keys.
5. Two-Factor Authentication (2FA) Best Practices

Standard passwords can be cracked, which is why Two-Factor Authentication (2FA) is mandatory for every crypto account. However, not all 2FA is created equal. SMS-based 2FA (getting a code via text) is vulnerable to "SIM swapping," where a hacker convinces your phone company to transfer your number to their device.
Instead, use app-based 2FA like Google Authenticator or Authy. For the highest level of security, use a physical security key like a YubiKey. These require a physical button press to authorize a login, making remote hacking nearly impossible. If you value your crypto, disable SMS 2FA immediately on all financial accounts.
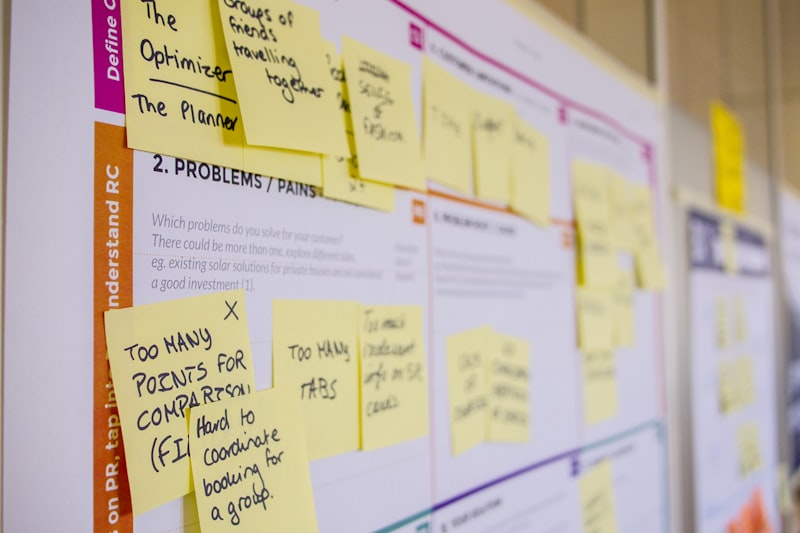
6. The Danger of "Pump and Dump" Schemes
Crypto is full of "get rich quick" promises. You'll often see new "meme coins" or low-cap tokens being hyped on Twitter (X) and Telegram. Many of these are "Pump and Dump" schemes where the creators buy a large amount of the coin, hype it to drive up the price, and then sell everything, leaving retail investors with a worthless asset. This is also called a "Rug Pull."
Before investing in any new project, do your own research (DYOR). Look for a legitimate team, a clear whitepaper, and actual utility. If the community is only talking about "going to the moon" and not about the technology, it's a red flag. Stick to established projects while you're still learning the ropes.
7. Smart Contracts: Reading the Fine Print
Decentralized Finance (DeFi) allows you to use "Smart Contracts" to lend, borrow, and trade without a bank. However, these contracts are only as good as their code. "Smart Contract Risk" is the danger that a bug in the code could be exploited by hackers. Many beginner investors lose money by interacting with unaudited or malicious contracts.
Never connect your main wallet to a site you don't trust. Use a "burner wallet" with only a small amount of funds for testing new DeFi apps. Check platforms like DeFi Llama to see which protocols have a long track record of security and multiple successful audits.
8. Public Wi-Fi and Wallet Access
Accessing your crypto wallet or exchange on public Wi-Fi (like at a cafe or airport) is a recipe for disaster. Hackers can use "man-in-the-middle" attacks to intercept the data being sent from your device. If you must check your account while on the go, use your mobile data or a trusted VPN (Virtual Private Network) to encrypt your connection.
Ideally, use a dedicated device just for your crypto activities. Keep it updated with the latest security patches and never use it for browsing untrusted sites or downloading pirated software. The more "boring" your crypto device, the safer your coins will be.
9. Social Engineering: The "I'm from Support" Scam
Scammers don't always use code; they use manipulation. You may receive a call or text from someone claiming to be from "Coinbase Support" or even "The IRS," telling you your account is being used for illegal activity and you must move your funds to a "safe wallet" they provide. Remember: no exchange or government agency will ever ask you to move your crypto to a new address.
Be suspicious of anyone who reaches out to you first. If you're worried about your account, go to the official website yourself and use their internal support system. Never trust a phone number or email address that hasn't been verified on the official site.
10. Long-term Security Habits: Regular Audits
Finally, security is not a one-time event; it's a habit. Every few months, do a "Security Audit" of your accounts. Check for any authorized apps that have access to your wallet and revoke ones you no longer use. Update your passwords, double-check that your cold storage devices are functioning, and remind yourself where your seed phrases are hidden.
The crypto landscape changes rapidly. New threats emerge almost every week. By staying informed and maintaining a "paranoid but patient" approach, you can enjoy the benefits of digital finance without falling victim to its predators. Your future self will thank you for the extra five minutes of caution today.
Our Take
At KUEEF, we see crypto as a tool for financial empowerment, but empowerment requires responsibility. The greatest risk in crypto isn't price volatility-it's human error. By slowing down, using cold storage, and never sharing your keys, you eliminate 99% of the risks. Don't let the fear of "missing out" lead you to skip security steps. In the world of digital wealth, slow is smooth, and smooth is fast. Secure your foundation first, and then build your future.